ICS/OT Cybersecurity Assessment
Structured security assessments for existing OT environments that have evolved through years of expansions, vendor integrations, and operational changes. We cut through the complexity to show you exactly where your risks are and what to do about them.
Assessing What Already Exists
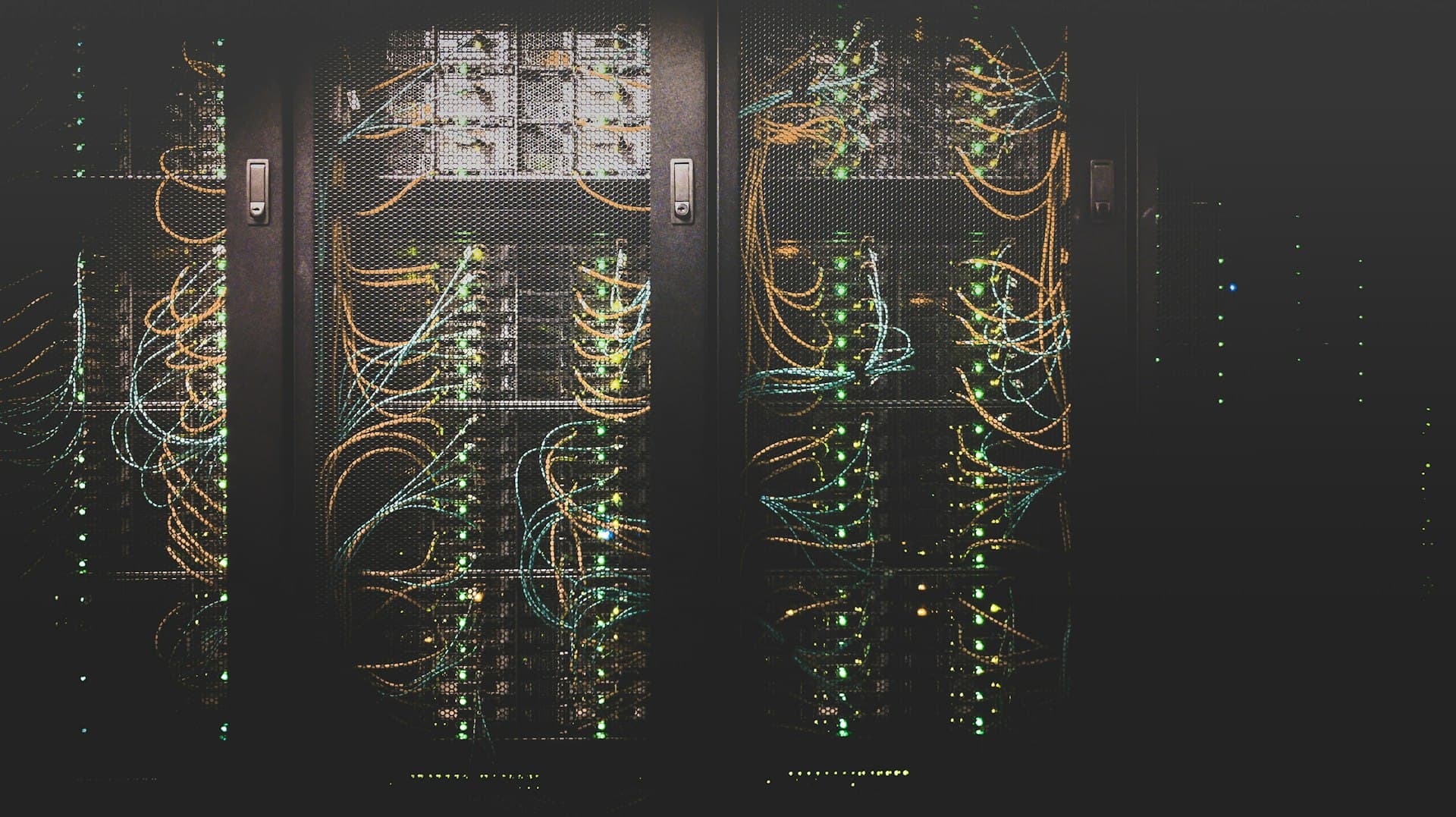
Most brownfield OT environments were never designed with cybersecurity in mind. Systems were connected for operational convenience: a historian linked to the DCS for trending, a VPN opened for a vendor who never left, a switch added during an expansion with no VLAN configuration. Over time, these decisions create an environment where nobody has a complete picture of what is connected, what is exposed, or where the real risks are. Our assessments provide that picture.
Risk Assessment
Structured risk identification, analysis, and treatment planning for industrial environments. Evaluates threats across safety, operational, financial, and regulatory dimensions using IEC 62443 and NIST CSF.
- Threat modeling and asset criticality analysis
- Impact and likelihood scoring across safety, operational, and financial dimensions
- Risk register with treatment plans aligned to maintenance windows
Vulnerability Assessment
Comprehensive identification and analysis of security weaknesses across OT networks, systems, and industrial assets using passive, non-intrusive methods that protect process availability.
- Passive network reconnaissance and asset discovery
- Correlation against NVD, ICS-CERT, and CISA KEV catalog
- Risk-prioritized findings based on operational impact, not just CVSS
Gap Assessment
Systematic evaluation against IEC 62443 requirements with maturity scoring across all foundational requirements, compliance mapping, and a prioritized remediation roadmap.
- IEC 62443 FR1-FR7 compliance mapping
- Maturity heat map: current state vs. target security level
- Phased remediation roadmap with effort and resource estimates
Penetration Testing
Controlled, OT-safe penetration testing that validates security controls without risking production systems, safety controllers, or process integrity.
- OT-safe rules of engagement protecting safety and production systems
- Lateral movement and privilege escalation testing across zone boundaries
- Full evidence documentation with remediation and retest guidance

Brownfield Security
Understanding what exists before deciding what to change
Frameworks We Align With
Industries Served
Frequently Asked Questions
We offer four assessment types: Risk Assessment for structured threat and impact analysis across safety, operational, and financial dimensions; Vulnerability Assessment using passive, non-intrusive methods to identify weaknesses without affecting production; Gap Assessment against IEC 62443 foundational requirements with maturity scoring and remediation roadmaps; and Penetration Testing with OT-safe rules of engagement that validate your security controls without risking production systems or safety controllers.
Start Your Assessment Engagement
Get in touch to discuss which assessment type is right for your OT environment and how we can scope the engagement for your organization.
