OT Vulnerability Assessment
Comprehensive identification and analysis of security weaknesses across OT networks, systems, and industrial assets. Our passive, non-intrusive approach delivers full visibility without risking the availability of the processes your systems control.
Finding What You Cannot See
Most OT environments have more devices on their network than anyone realizes. Engineering teams estimate 150 assets; passive discovery reveals 230. The gap includes forgotten test equipment, undocumented vendor laptops, rogue wireless bridges, and controllers running firmware versions with known exploits.
An OT Vulnerability Assessment builds the foundational asset inventory and risk picture you need before any security investment makes sense. Without knowing what is on your network, what firmware it runs, and what vulnerabilities it carries, remediation is guesswork.
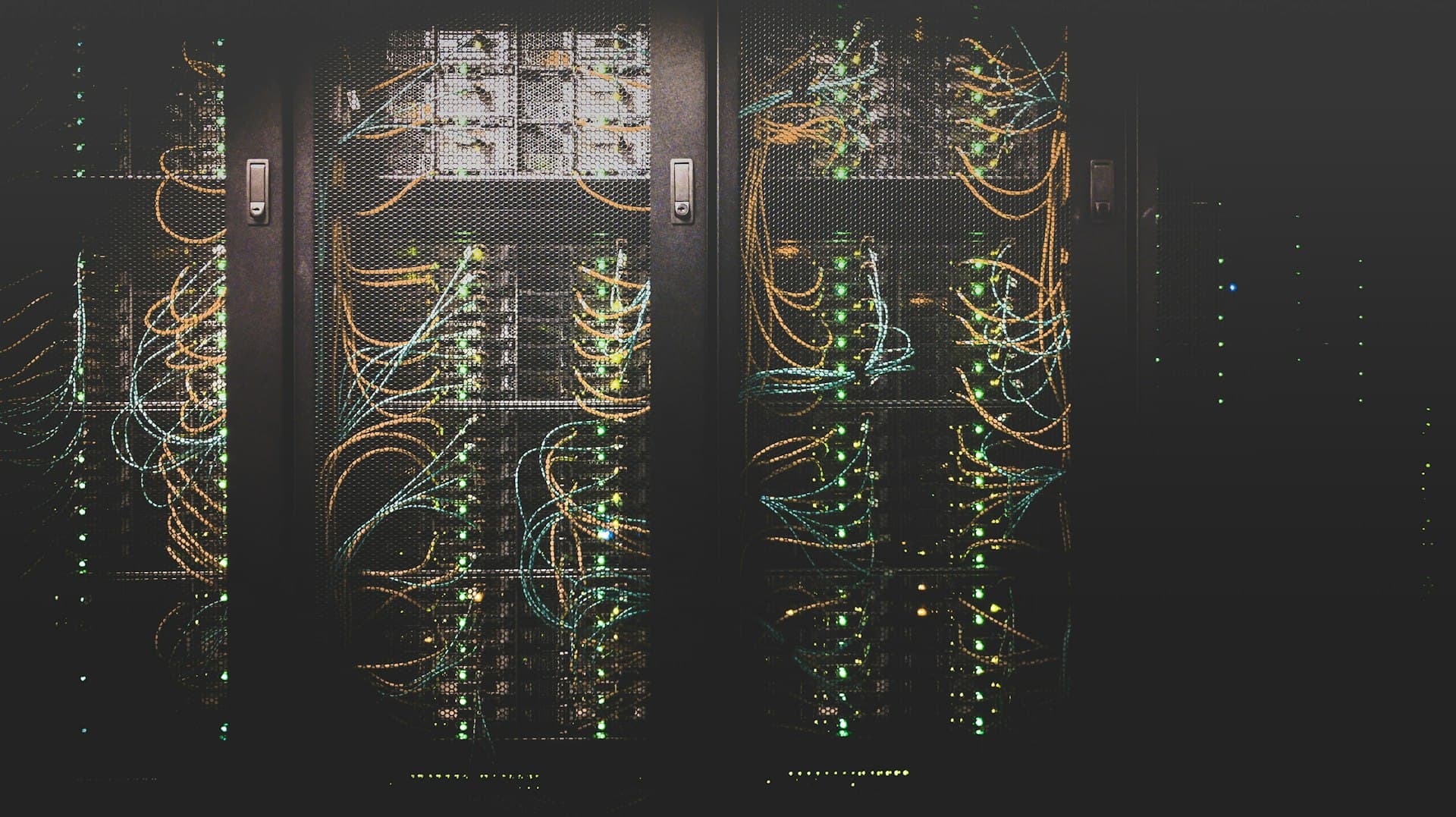
Our approach is built for environments where a single misplaced packet can crash a legacy PLC. We use network TAPs and SPAN ports for passive traffic capture, correlate findings against NVD, ICS-CERT, and CISA KEV databases, and score every vulnerability using an OT-adapted risk model that prioritizes operational impact over raw CVSS numbers.
What We Assess
- PLCs, RTUs, and field devices
- SCADA and DCS servers
- HMI and engineering workstations
- Historian and data servers
- Industrial networking equipment
- Remote access infrastructure
- IT/OT network boundaries and DMZs
Non-Intrusive Assessment
Passive techniques that deliver visibility without disrupting operations
Engagement Methodology
Each phase is designed to deliver measurable progress while respecting the operational constraints of live industrial environments.
Scope Definition and Planning
Define the assessment boundary, target systems, and objectives in collaboration with plant operations and engineering teams. Identify constraints including maintenance windows, production schedules, and safety-critical systems that require special handling. Establish communication protocols and escalation procedures.
Entry Point Analysis
Map all ingress and egress points to the OT environment including IT/OT boundaries, remote access connections, vendor links, DMZ services, and wireless access points. Evaluate the security posture of each entry point to understand how an attacker could reach industrial systems from external or adjacent networks.
Passive Network Reconnaissance
Deploy passive monitoring to discover assets, map network topology, and identify communication flows without generating traffic on the OT network. Catalog all discovered devices including PLCs, RTUs, HMIs, historians, engineering workstations, and networking equipment. Build a comprehensive asset inventory with firmware versions, protocols, and network relationships.
Firewall and Network Device Review
Analyze firewall rule sets, switch configurations, and VLAN assignments to evaluate segmentation effectiveness. Identify overly permissive rules, unused access paths, and configuration drift from intended policy. Verify that zone boundaries enforce the principle of least privilege for inter-zone communication.
Vulnerability Identification
Correlate discovered assets and firmware versions against vulnerability databases including NVD, ICS-CERT advisories, vendor security bulletins, and the CISA Known Exploited Vulnerabilities catalog. Identify missing patches, insecure protocols, default credentials, and configuration weaknesses specific to the OT environment.
Risk-Based Prioritization
Score each vulnerability using an OT-adapted risk model that accounts for exploitability, operational impact, safety consequences, and compensating controls already in place. Standard CVSS scores are adjusted to reflect the realities of industrial environments where availability and safety outweigh confidentiality.
Remediation Roadmap and Reporting
Deliver a structured report with a three-tier remediation roadmap: immediate actions for critical exposures, medium-term improvements aligned to maintenance schedules, and strategic initiatives for architectural enhancements. Include an executive summary suitable for board-level reporting alongside full technical detail for engineering teams.
Service Deliverables
- OT asset inventory with network map
- Detailed vulnerability report with OT-adapted risk ratings
- Network topology and segmentation analysis
- IEC 62443 gap analysis at component and system level
- Prioritized three-tier remediation roadmap
- Executive summary for board-level reporting
Frameworks We Align With
Industries Served
Start Your OT Vulnerability Assessment Engagement
Tell us about your industrial environment and we will scope an engagement tailored to your systems, constraints, and objectives.
