Youcan'tprotectwhatyouaren'tawareof
Cybersecurity consulting for SCADA, DCS, PLC, and safety systems across oil and gas, energy, manufacturing, and critical infrastructure. Assessment, design, implementation, and monitoring.
Proven OT Security Results
Platforms and Vendors We Work With
Industrial Vendors
















OT Security Platforms




















Our Clients


































ICS/OT Cybersecurity Services
From greenfield architecture design to brownfield assessment and hands-on implementation, every service is engineered for environments where safety and uptime are non-negotiable.
ICS/OT Cybersecurity Design
Cybersecurity architecture for new-build ICS/OT projects, integrated from FEED through FAT, SAT, commissioning, and operational handover.
ICS/OT Cybersecurity Assessment
Risk, vulnerability, IEC 62443 gap, and penetration testing assessments for brownfield OT environments using passive, non-intrusive methods.

ICS/OT Cybersecurity Implementation
Hands-on deployment of IDS/IPS, firewall rules, network segmentation, switch hardening, and secure remote access within live production environments.

ICS/OT Product Security
Secure development lifecycle, architecture review, and IEC 62443-4-1/4-2 certification readiness for OEM industrial product manufacturers.

ICS/OT SOC Deployment
OT Security Operations Center build: use case definition, SIEM configuration, OT-specific detection rules, incident playbooks, and team handover.

ICS/OT Security Training
Structured OT cybersecurity training programs: awareness training, incident response tabletop exercises, and hands-on testbed development for industrial organizations.

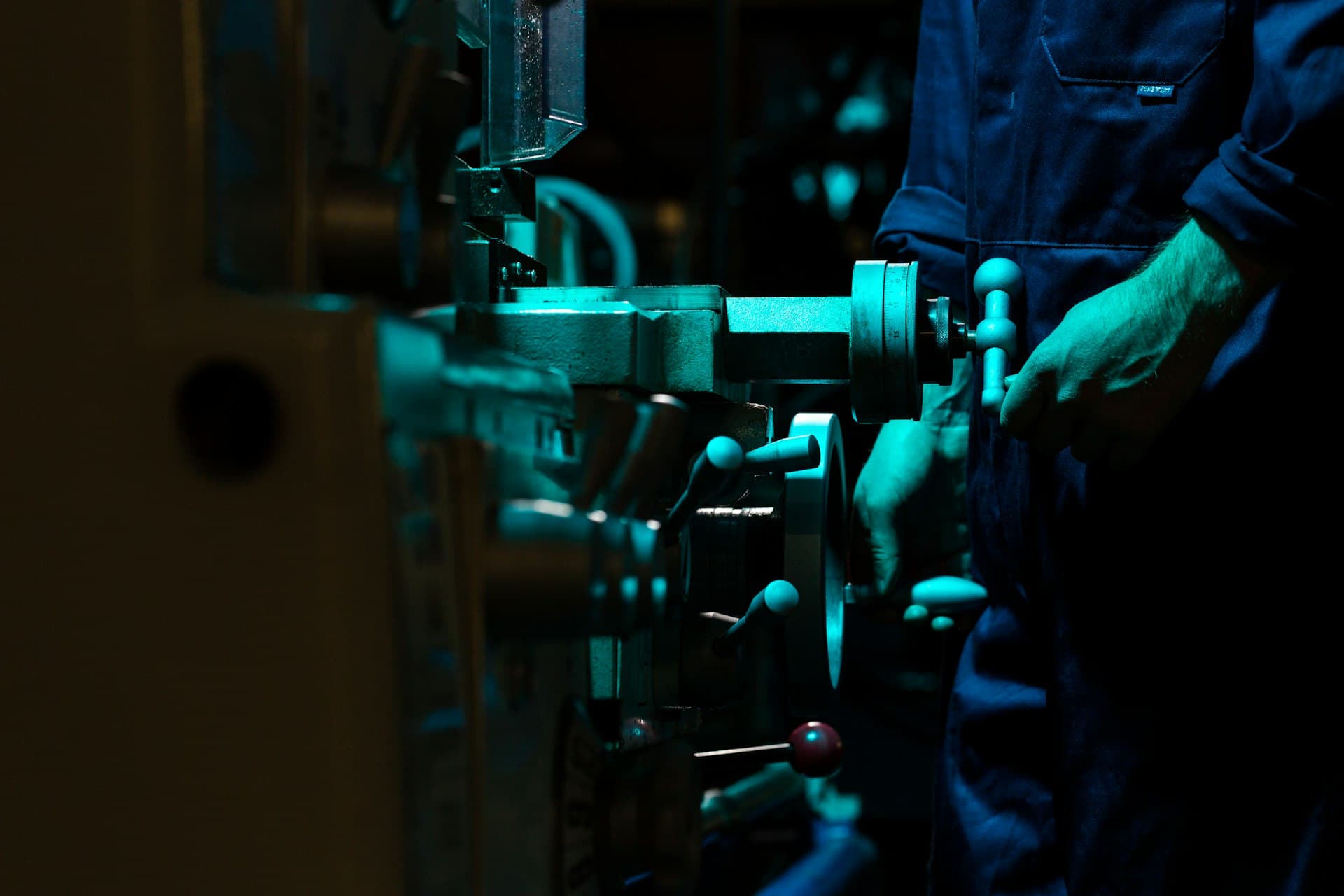
Purpose-Built for
Industrial Security
I built Beacon Security because the industrial world deserved better than recycled IT security wrapped in a new label. Every time I saw an OT environment being assessed with tools and thinking designed for corporate networks, I knew something had to change. So we built a team that lives and breathes industrial cybersecurity. Engineers who understand process control, who know why you never touch a safety system during a batch run, and who can design a security architecture around operational reality, not against it. What makes us different is simple: we don't adapt IT solutions for OT. We build OT-native security from the ground up. Our team combines hands-on industrial experience with advanced threat intelligence tailored specifically to control system environments. We are not here to check a compliance box. We are here to make sure your operations stay safe, stay running, and stay ahead of the threats that most security firms are only beginning to understand.
Built for the Industries We Serve
A refinery DCS operates nothing like an automotive PLC network. We bring hands-on knowledge of the systems, protocols, and safety constraints specific to each sector.

Oil and Gas
Protecting upstream, midstream, and downstream OT environments across exploration, production, refining, pipelines, terminals, storage, and distribution operations.

Energy
Securing thermal power plants, renewable energy installations including solar, wind, and hydro, and power generation control systems against evolving cyber threats.

Electrical
Protecting transmission networks, distribution systems, substations, grid infrastructure, switchyards, and electrical network operations from cyber threats.

Manufacturing
Industrial cybersecurity for discrete and process manufacturing, automation systems, robotics, production lines, and smart factory environments.

Chemicals
Safety-first OT cybersecurity for chemical processing, fertilizers, specialty chemicals, batch and continuous processing, and plant operations.

Automotive
Securing OEM assembly lines, tier supplier facilities, EV battery manufacturing, robotic systems, and connected production environments.
Real-World OT Security Delivered
Representative examples of how Beacon Security approaches OT cybersecurity challenges across industrial sectors.
An oil and gas operator with 280+ OT assets across 3 production sites was running uncontrolled RDP and SSH sessions into SCADA, DCS, and safety systems. A vendor accidentally modified a compressor setpoint outside their scope during an unmonitored session, triggering an immediate board-level escalation.
- 14 persistent VPN tunnels across 9 organizations, two belonging to vendors with expired contracts
- Shared credentials held by 47 individuals including 11 who had changed roles or left their companies
- 9 of 14 tunnels could reach safety-related systems with no session visibility or recording
- No time restrictions, no user segregation, no scheduled access windows on any tunnel
Beacon Security deployed a secure remote access gateway in the Level 3.5 DMZ with four-tier user segregation, full session recording, and role-based access controls. Every direct RDP/SSH path to production was eliminated.
- Redundant gateway in Level 3.5 DMZ. Remote users never get a direct network path to production systems
- Four-tier segregation: internal operators, trusted vendors, untrusted access with live supervision, and break-glass emergency
- Full session recording with keystroke capture, secure file transfer with malware scanning, and live monitoring dashboard
- Scheduled access windows replacing 24/7 persistent connections. Access outside windows requires operations approval
- 47 individual credentials issued across 9 organizations, replacing every shared account
All 14 legacy VPN tunnels permanently decommissioned. Active connection hours reduced by 78%. Three unauthorized access attempts blocked within 60 days. Session recordings provided root-cause evidence for two operational issues that would have gone unexplained under the old model.
Aligned with Global OT Security Mandates
Our methodologies align with every major OT cybersecurity standard, from international frameworks to regional regulatory mandates, giving clients confidence across global operations.
IEC/ISA 62443
The gold standard for Industrial Automation and Control Systems (IACS) security. We apply IEC/ISA 62443 to define Security Levels (SL1-SL4), establish security zones and conduits, and drive systematic risk reduction across OT environments.
NIST SP 800-82
NIST Special Publication 800-82 provides guidance on securing Industrial Control Systems (ICS). Our assessments align with its recommended security architecture, defense-in-depth strategies, and ICS-specific risk management practices.
OTCC
The Operational Technology Cybersecurity Controls framework by Saudi Arabia's National Cybersecurity Authority (NCA). We support organizations operating in the Kingdom to achieve and maintain OTCC compliance across critical sectors.
ECC
The Essential Cybersecurity Controls (ECC) framework mandated by Saudi Arabia's NCA for all government and critical sector organizations. We help entities meet ECC requirements with OT-specific implementation guidance.
EU Cyber Resilience Act
The EU Cyber Resilience Act introduces mandatory cybersecurity requirements for connected products and software. We advise manufacturers and operators of OT systems on meeting CRA obligations for products with digital elements.
NIS2 Directive
The EU Network and Information Security Directive 2 mandates cybersecurity risk management and incident reporting for essential and important entities, including energy, transport, and manufacturing. We help industrial operators meet NIS2 obligations for their OT environments.
DESC ICS Standard
The Dubai Electronic Security Center ICS security standard establishes mandatory cybersecurity requirements for industrial control systems operating in Dubai. We support organizations in achieving DESC ICS compliance across critical infrastructure and utility sectors.
Qatar NCSA Framework
The Qatar National Cyber Security Agency framework defines cybersecurity requirements for critical national infrastructure operators. We assist organizations in Qatar to align their OT security programmes with NCSA mandates across energy, utilities, and industrial sectors.
NCIIPC Guidelines
The National Critical Information Infrastructure Protection Centre under the Government of India issues guidelines for protecting critical information infrastructure. We help Indian industrial operators implement NCIIPC recommendations for their OT and SCADA environments.
All Beacon Security engagements are scoped to applicable framework requirements based on your sector, geography, and regulatory obligations.
Common Questions
Answers to the most common questions about OT cybersecurity services, standards, and how Beacon Security can help your organization.
Have a question not covered here? Our team is happy to discuss your specific environment and requirements.
Contact us directlyOT cybersecurity protects the control systems that run physical processes: PLCs, SCADA, DCS, and safety controllers. The priorities are fundamentally different from IT. In IT, confidentiality comes first. In OT, safety and availability take precedence because a compromised controller can cause equipment damage, environmental releases, or injuries. OT systems also operate under unique constraints. They run 24/7 with no maintenance windows, use industrial protocols like Modbus TCP, DNP3, and OPC UA that were designed without authentication, have lifecycles of 15 to 30 years, and often cannot be patched without halting production. A firewall rule that makes sense in a corporate network can shut down a reactor or trip a turbine in an OT environment. Beacon Security works exclusively in OT. Every assessment, design, and implementation we deliver is built around these operational realities, not adapted from IT playbooks.

Your OT Environment Deserves
Expert Protection
IT security tools were not built for Modbus, OPC, or safety-rated controllers. Get a dedicated OT cybersecurity team that understands industrial protocols, control system architecture, and the operational constraints of your environment.

